Suspected US government tool leak! Google reveals new type of cryptocurrency scam iPhone attack chain

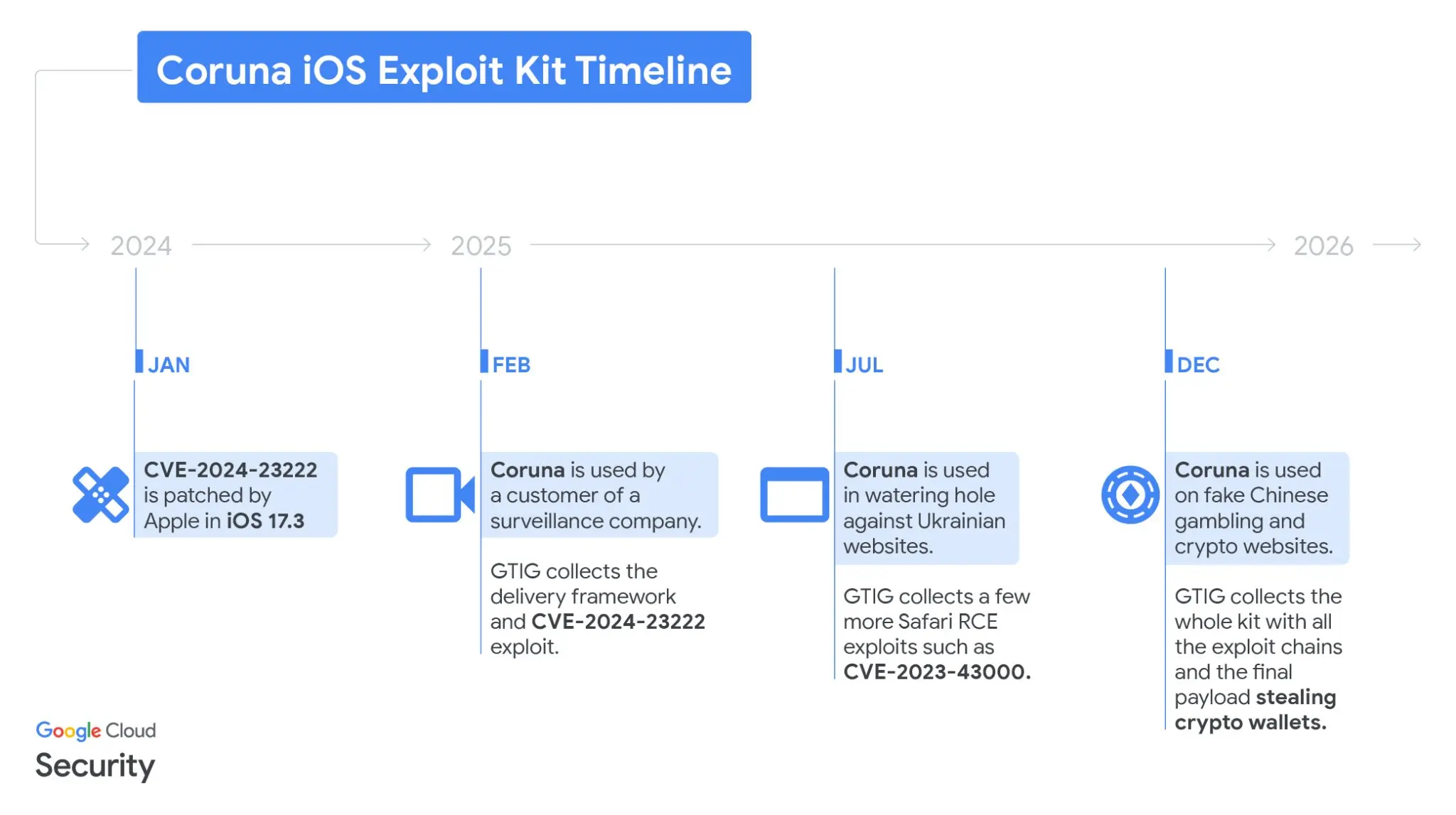
The Google Threat Intelligence Group (GTIG) released a report on Wednesday revealing that a new iPhone vulnerability exploitation toolkit called Coruna has been deployed in large-scale cryptocurrency scam operations. Security firm iVerify disclosed that Coruna may originate from the U.S. government and was repurposed by adversaries and cybercriminal groups after losing control.
Technical Analysis of the Coruna Toolkit: How It Targets and Steals Crypto Wallets
(Source: Mandiant)
Coruna employs JavaScript technology to fingerprint iOS devices accessing fake websites, automatically deploying exploit code once the target version is identified. Once the device is compromised, the toolkit systematically searches for the following sensitive information:
Crypto Mnemonics: Locally stored text containing keywords like “backup phrase” and “seed phrase”
Popular Crypto Applications: Targeting decentralized wallet apps such as Uniswap and MetaMask to extract keys or account data
Financial Account Information: Simultaneously searching for bank accounts and other sensitive payment data
GTIG confirmed that Coruna is incompatible with the latest iOS versions and strongly recommends all iPhone users update their systems immediately. Those unable to upgrade should enable Apple’s “Lockdown Mode,” which Apple states can effectively defend against highly sophisticated targeted attacks.
From Intelligence Operations to Crypto Scam Websites: Two Propagation Paths of Coruna
GTIG’s tracking shows that Coruna has gone through two distinct phases of use. Initially, suspected Russian intelligence used compromised Ukrainian websites to target specific geographic iPhone users, exhibiting typical intelligence-gathering behavior.
In December 2025, GTIG discovered the same JavaScript framework within a large network of fake Chinese financial websites, including a counterfeit site mimicking the cryptocurrency exchange WEEX. When iOS users visit these fake sites, the toolkit automatically extracts financial information in the background, prioritizing crypto wallet mnemonics, posing a direct threat to assets and transforming the original intelligence tool into a large-scale cryptocurrency scam operation.
Attribution Controversy: Is It a U.S. Government Tool or Commercial Spyware?
The most debated aspect of this incident is Coruna’s potential origin. iVerify co-founder Rocky Cole told WIRED that the toolkit “is highly complex, developed at a cost of millions of dollars, and features modules publicly attributed to the U.S. government,” suggesting this may be “the first case of a U.S. government tool being hijacked and exploited by adversaries and cybercriminal groups.”
However, Kaspersky’s chief security researcher disagrees, stating that “no evidence of actual code reuse has been found in the published reports” to support this attribution. GTIG also did not disclose the identity of the initial monitoring client using Coruna, leaving the attribution question unresolved for now.
Frequently Asked Questions
Does the Coruna toolkit affect the latest iPhone versions?
GTIG confirms that all five exploit chains of Coruna target iOS versions 13.0 to 17.2.1, which are incompatible with the current latest iOS system. All iPhone users should update their systems immediately. Those unable to upgrade should enable “Lockdown Mode” to reduce risk.
How did Google discover Coruna being used in crypto scams?
In February 2025, GTIG identified parts of the toolkit’s code, tracing it back to the same JavaScript framework on compromised Ukrainian websites. Later, it was fully deployed across a large network of fake Chinese websites mimicking WEEX, confirming the toolkit’s transition from intelligence gathering to large-scale crypto scam tool.
How can I protect my crypto mnemonics from being stolen by such tools?
Besides updating iOS immediately, it is recommended to store mnemonics offline on cold storage devices (like hardware wallets or paper backups). Avoid storing mnemonics in plaintext on any internet-connected device, and verify the authenticity of all crypto-related websites to prevent visiting untrusted financial sites.