Como funciona o idOS? Uma análise detalhada de todo o processo, desde o armazenamento de dados até à aprovação de acesso
Em ambientes de internet tradicionais, os dados de identidade dos utilizadores costumam ser armazenados centralmente pelas plataformas, o que gera problemas como silos de dados, verificações repetidas e fugas de privacidade. Esta realidade é especialmente crítica nos serviços financeiros, onde é frequente os utilizadores terem de concluir a KYC (Verificação de identidade) em várias plataformas distintas. O resultado é uma menor eficiência e um risco acrescido de uso indevido dos dados. Com a expansão das aplicações em Blockchain, este modelo tornou-se um verdadeiro obstáculo à experiência do utilizador e à conformidade em Web3.
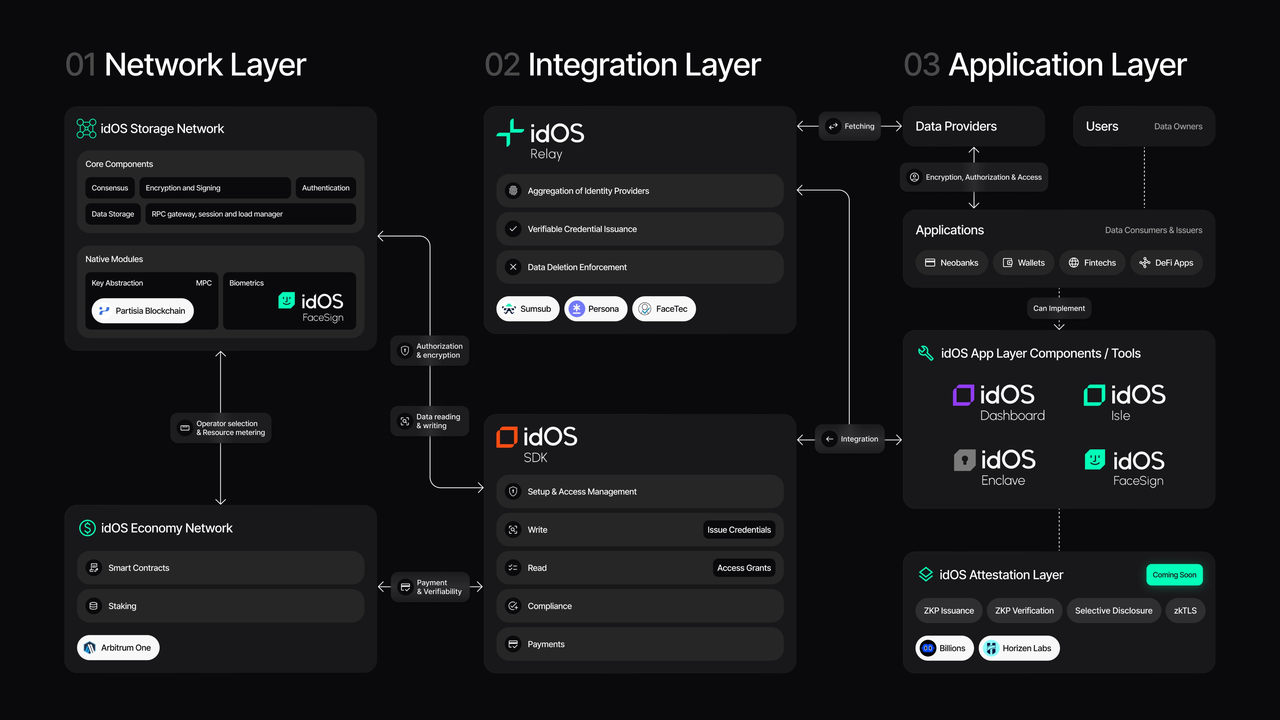
idOS foi criado para resolver estes desafios, atuando como a “camada descentralizada de dados de identidade” para Web3. Ao colocar o controlo dos dados de identidade nas mãos dos utilizadores e ao adotar armazenamento encriptado com acesso sujeito a aprovação, o idOS permite a partilha segura e transparente de informações de identidade entre várias aplicações. Esta abordagem não só eleva a experiência do utilizador, como também oferece um suporte essencial para stablecoins, DeFi e aplicações financeiras conformes.
Lógica central do idOS: do armazenamento à aprovação
O idOS gere o ciclo de vida dos dados em cinco etapas fundamentais: geração → armazenamento → pedido → aprovação → utilização.
Sempre que um utilizador acede a uma aplicação, é necessário concluir um processo de verificação de identidade, normalmente realizado por entidades profissionais de verificação (Issuers), como prestadores de serviços de KYC. Após a verificação, os dados de identidade do utilizador são encriptados e armazenados na rede descentralizada do idOS.
Ao contrário das bases de dados tradicionais, estes dados não ficam sob o controlo de uma única plataforma. São distribuídos de forma encriptada por vários nodos da rede. O utilizador gere as autorizações de acesso através da sua Chave privada ou credenciais de identidade, assegurando a verdadeira autocustódia dos seus dados.
Quando outra aplicação (Consumer) necessita de utilizar estes dados de identidade, não pode aceder diretamente aos mesmos — tem de submeter um pedido de acesso. O pedido define o tipo de dados necessários e o objetivo de utilização, como “verificar se o utilizador concluiu KYC” ou “confirmar o país do utilizador”.
Neste momento, ativa-se o mecanismo central do idOS — Access Grant. O utilizador pode aprovar ou rejeitar o pedido e definir o âmbito da aprovação (por exemplo, campos específicos ou limites temporais). Só após aprovação é que a aplicação recebe os dados desencriptados ou a prova de verificação.
Este processo garante que o utilizador mantém sempre o controlo dos seus dados e permite a reutilização da identidade entre plataformas.
Armazenamento de dados no idOS: encriptado e distribuído por design
O idOS alia encriptação a uma arquitetura distribuída para armazenamento dos dados. Os dados de identidade são encriptados antes de serem registados na rede, garantindo que, mesmo ao nível do nodo, a informação em texto simples permanece inacessível.
Os nodos da rede de armazenamento asseguram a disponibilidade e segurança dos dados, mas não têm capacidade de desencriptação. Esta arquitetura protege a privacidade e elimina o risco de ponto único de falha típico do armazenamento centralizado.
Os dados são habitualmente registados em formato estruturado — como documentação de identidade, endereço ou estado de conformidade — permitindo integração normalizada entre diferentes aplicações. Esta estrutura serve de base para dados de identidade composíveis.
Access Grant: o mecanismo central de aprovação do idOS
O Access Grant é uma das funcionalidades mais relevantes do idOS, definindo as regras de acesso e utilização dos dados.
Todo o acesso exige aprovação do utilizador, com controlo granular. O utilizador pode definir não só se aprova o acesso, mas também:
-
Que dados podem ser acedidos
-
O período de tempo autorizado
-
Se é permitida a utilização repetida
Este modelo funciona como uma “camada de permissões de dados”, separando a propriedade dos dados dos direitos de utilização e permitindo uma gestão flexível da privacidade.
Para as aplicações, isto significa não ter de armazenar dados sensíveis dos utilizadores; basta solicitar aprovação sempre que necessário. Assim, reduzem-se significativamente os riscos de conformidade de dados.
Participantes e fluxo de dados
A rede idOS integra quatro participantes principais, constituindo um sistema de fluxo de dados completo.
Os utilizadores detêm e controlam os seus dados, gerindo aprovações e permissões de acesso.
Os Issuers validam os dados, gerando informações de identidade fidedignas como KYC ou verificações de conformidade.
Os Consumers utilizam os dados — como plataformas de negociação, aplicações de stablecoin ou protocolos DeFi — mediante pedido de aprovação.
Os operadores de nodos asseguram o funcionamento da rede, garantindo o armazenamento e a disponibilidade dos dados.
O fluxo típico de dados: Utilizador → Issuer (verificação) → Armazenamento encriptado → Pedido do Consumer → Aprovação do utilizador → Utilização dos dados.
Este processo pode repetir-se em diferentes aplicações, permitindo a reutilização dos dados de identidade em todo o ecossistema.
Exemplo de fluxo de trabalho: reutilização de KYC com idOS
O valor do idOS revela-se sobretudo na reutilização do KYC.
Após o utilizador concluir a verificação de identidade numa plataforma, os dados ficam armazenados na rede idOS. Ao aceder a outra plataforma que exige KYC, não é necessário submeter novamente a documentação — basta autorizar a utilização dos dados existentes através do idOS.
Quando a nova plataforma submete um pedido e o utilizador aprova, o sistema devolve o resultado da verificação ou a informação necessária. Este processo decorre normalmente em segundo plano, proporcionando uma experiência de “verificação com um clique”.
Este modelo reduz custos e atritos de verificações repetidas, ao mesmo tempo que reforça a consistência dos dados e a conformidade.
Diferenças principais: idOS vs. sistemas de identidade tradicionais
A diferença fundamental entre o idOS e os sistemas centralizados de identidade tradicionais está no controlo e acesso aos dados.
Nos sistemas tradicionais, as plataformas controlam os dados dos utilizadores, limitando o poder de decisão destes. No idOS, o utilizador controla os seus dados e só concede acesso mediante aprovação.
Estes sistemas tradicionais não permitem reutilização entre plataformas, enquanto o idOS viabiliza a portabilidade da identidade através de uma camada de dados unificada.
Estas diferenças fazem do idOS a solução ideal para o ecossistema colaborativo e multiaplicação de Web3.
Resumo
O idOS recorre a armazenamento encriptado e acesso baseado em aprovação para construir uma rede descentralizada de dados de identidade, permitindo aos utilizadores controlar e reutilizar os seus dados com segurança em diferentes aplicações. Os principais pontos fortes são a redução dos custos de verificação de identidade, o reforço da privacidade e a oferta de uma infraestrutura de identidade escalável para stablecoins e finanças on-chain.
Perguntas frequentes
O que é o idOS Access Grant?
O Access Grant é um mecanismo de aprovação de acesso a dados que permite ao utilizador decidir quem pode aceder aos seus dados de identidade e qual o âmbito desse acesso. É o pilar da soberania de dados no idOS.
O idOS armazena dados em texto simples dos utilizadores?
Não. Todos os dados são encriptados antes de serem armazenados na rede. Os nodos não têm acesso à informação em texto simples; a desencriptação ou os resultados de verificação só são fornecidos após aprovação do utilizador.
Como é que o idOS permite a reutilização de KYC?
Ao encriptar e armazenar os dados de identidade verificados na rede, o utilizador pode autorizar outras plataformas a utilizar esses dados, evitando submissões repetidas.
Em que é que o idOS difere das bases de dados tradicionais?
As bases de dados tradicionais são controladas pelas plataformas, enquanto o idOS utiliza armazenamento descentralizado e aprovações do utilizador, transferindo o controlo dos dados das plataformas para os utilizadores.
Que aplicações utilizam o idOS?
O idOS é utilizado sobretudo em cenários que exigem verificação de identidade, incluindo plataformas de stablecoin, protocolos DeFi e serviços financeiros conformes.
Artigos relacionados

Modelo Económico do Token ONDO: De que forma impulsiona o crescimento da plataforma e o envolvimento dos utilizadores?
Análise de tokenomics do JTO: distribuição, casos de utilização e valor de longo prazo
Jito vs Marinade: Análise comparativa dos protocolos de Staking de liquidez na Solana
Análise das Fontes de ganhos de USD.AI: como os empréstimos de infraestrutura de IA geram retorno
Tokenomics do USD.AI: análise aprofundada dos casos de utilização do token CHIP e dos mecanismos de incentivos