What Is Sign (SIGN)? Definition, Technical Principles, and Key Use Cases Explained
Unlike traditional blockchain systems that primarily focus on asset transactions, Sign aims to address the challenge of "trusted data" on Web3. In decentralized environments, information such as identity, contributions, governance records, reputation, or compliance status is often difficult to verify consistently. Sign introduces a standardized onchain attestation mechanism that allows different applications to generate and verify trusted credentials, forming a shared data infrastructure.
From the perspective of blockchain infrastructure development, Sign represents an important exploration into the identity and data infrastructure layer of Web3. By introducing onchain attestations, verifiable credentials, cross-chain data synchronization, and modular architecture, Sign transforms identity and behavioral records into composable onchain resources. This provides a more reliable data foundation for scenarios such as DAO governance, onchain identity, airdrop verification, and onchain reputation systems.
Sign’s Background and Positioning
 Source: Sign Official Website
Source: Sign Official Website
As the Web3 ecosystem expands, blockchain applications are evolving from simple asset transactions toward more complex social and economic systems. In this transition, trusted identity and trusted data are becoming critical infrastructure.
For example:
-
DAOs need to verify member contributions
-
Airdrop projects need to identify genuine users
-
DeFi protocols need to recognize high-reputation participants
-
Web3 communities need onchain reputation systems
However, most blockchain systems still lack a standardized mechanism to record and verify this type of information. The Sign protocol emerged in response to this challenge. Its core objective is to build an onchain attestation network that allows different applications to generate, store, and verify digital credentials.
These credentials can represent many forms of onchain or offchain information, such as user identity verification, behavioral records, project contributions, governance voting history in DAOs, or an individual's activity history across blockchain networks. Together, they help create a more complete and verifiable digital identity and data system.
By structuring and anchoring this information onchain, Sign aims to become a trusted data infrastructure layer for the Web3 era.
Core Components and Technical Features of Sign
The Sign protocol is built around three key components.
- Attestation (Proof System)
Attestation is the core mechanism of Sign. It records a statement made by one entity about another entity.
Examples include:
-
A DAO confirming that a user is a core member
-
A protocol verifying that a user completed a specific task
-
An institution confirming that a user passed KYC verification
These attestations are cryptographically recorded and remain verifiable.
- Schema (Attestation Structure)
To ensure compatibility across different applications, Sign uses Schema structures to define the format of attestations.
Examples include:
-
Identity attestation schema
-
Contribution attestation schema
-
Governance attestation schema
Schemas allow different applications to rely on a shared data standard.
- Verification Network
The Sign protocol allows third-party verification nodes to validate and synchronize attestations, improving data reliability while reducing single point of failure risks. This design enables attestation data to be stored onchain while also allowing efficient querying through offchain systems.
How the Sign Protocol Works
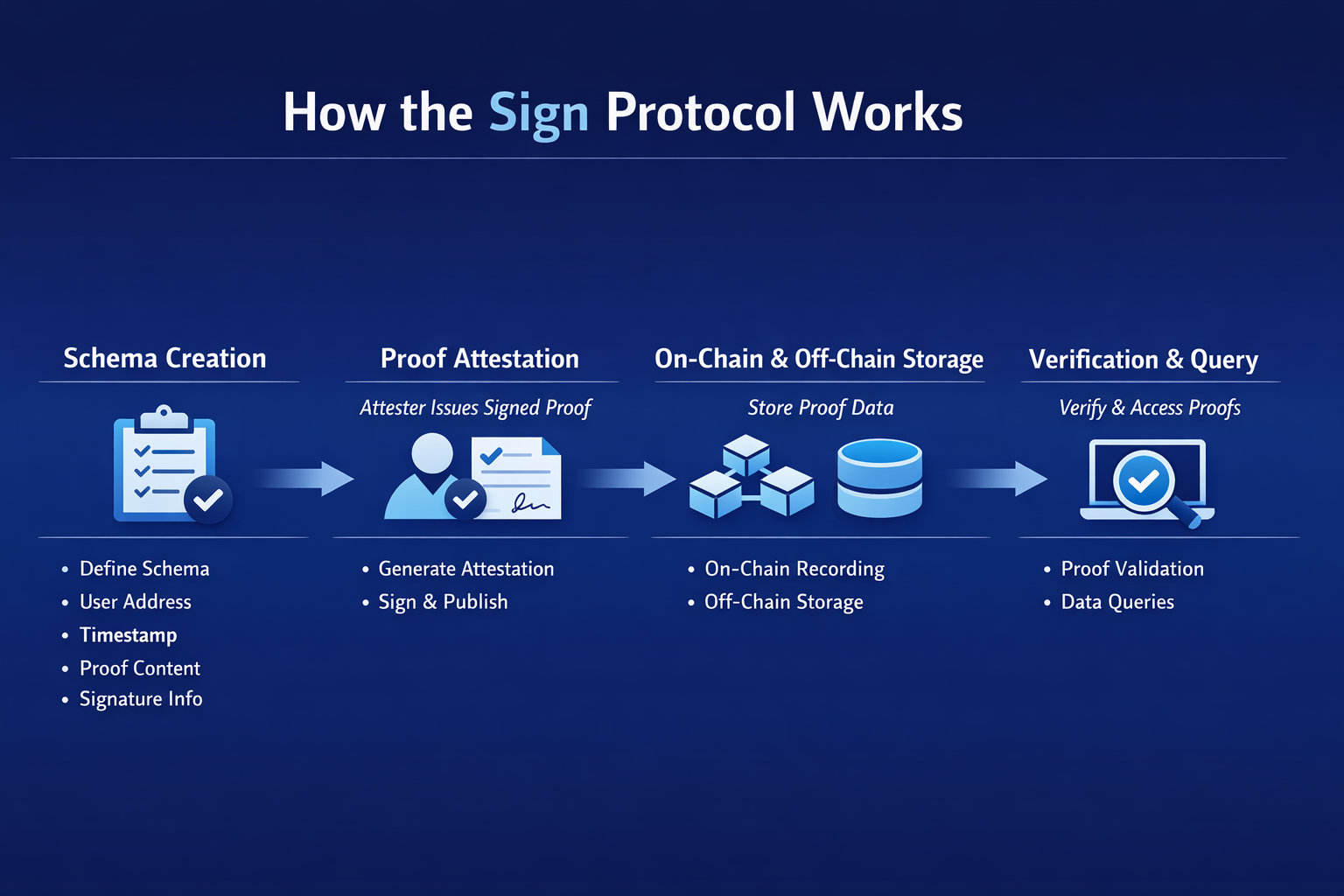
The operational logic of Sign can be understood as a full lifecycle process: attestation creation → storage → verification → usage.
Attestation Creation Process
The process of generating attestations typically includes the following steps.
- Create a Schema
Developers first define the attestation structure, which may include:
-
User address
-
Timestamp
-
Attestation content
-
Signature information
- Publish an Attestation
The attestation issuer, known as the Attester, generates a signature and submits the attestation.
- Onchain Recording
The attestation may be written directly to the blockchain or recorded using offchain storage solutions.
- Verification and Query
Other applications can verify attestations by calling the Sign protocol API or querying onchain data.
Through this process, any application can generate trusted credentials.
Cross-Chain Interoperability Mechanism
The Web3 ecosystem is increasingly multi-chain. As a result, Sign was designed with cross-chain data considerations in mind.
Sign’s cross-chain mechanism primarily includes:
-
Cross-chain attestation synchronization, allowing attestation data to be shared between different blockchains
-
Unified verification interfaces, enabling developers to use the same verification logic across multiple chains
-
Multi-chain schema compatibility, ensuring consistent data structures across networks
This cross-chain capability means that identity or behavioral records from one chain can be verified on another.
For example:
-
A reputation score from Ethereum could be recognized by an application on BNB Chain
-
Activity on Layer2 networks could be used by applications on a main chain
This significantly improves the portability of Web3 identity systems.
Modular Architecture
The Sign protocol adopts modular architecture to support diverse application requirements.
The primary modules include:
-
Attestation Layer, responsible for generating and managing attestations
-
Data Layer, responsible for storing schemas and attestation records
-
Verification Layer, responsible for validating the authenticity of attestations
-
Developer Interfaces (API / SDK), enabling developers to integrate the protocol easily
The advantages of modular architecture include:
-
Support for multiple storage methods
-
Compatibility with both onchain and offchain attestations
-
Improved scalability
Developers can choose different components depending on their needs.
SIGN Token Governance and Economic Model
The SIGN token is the core governance and incentive asset within the Sign protocol ecosystem.

Source: Sign Official Website
Its primary functions include:
- Protocol Governance
SIGN holders can participate in governance voting on matters such as:
-
Parameter adjustments
-
Protocol upgrades
-
Treasury usage
- Network Incentives
SIGN may be used to reward:
-
Verification nodes
-
Data providers
-
Ecosystem developers
- Ecosystem Payments
In certain applications, SIGN may be used to pay for:
-
Attestation generation fees
-
Data query fees
-
API usage fees
This design positions SIGN as an important economic incentive mechanism for the protocol’s operation.
Sign Ecosystem and Core Use Cases
As demand for Web3 identity and data infrastructure grows, Sign’s application scenarios continue to expand.
- Web3 Identity Systems
Sign can serve as infrastructure for decentralized identity (DID) systems.
Users may hold multiple attestations, such as:
-
Community membership status
-
Project contribution history
-
NFT ownership history
Together, these records form a user’s onchain identity profile.
- DAO Governance
DAOs can use Sign to record:
-
Member contributions
-
Voting history
-
Role permissions
This helps create more transparent governance structures.
- Airdrop Qualification and Sybil Resistance
Many projects need ways to identify real users.
Sign’s attestation mechanism can support:
-
User eligibility verification
-
Airdrop filtering
-
Activity proofs
This helps reduce the risk of Sybil attacks.
- Onchain Reputation Systems
By recording user behavior over time, reputation scores can be established onchain.
Examples include:
-
DeFi credit reputation
-
Community contribution scores
-
Developer contribution records
These data sets can be shared across different applications.
Differences Between Sign and Traditional Identity Management Systems
Traditional identity systems usually rely on centralized institutions to manage user data. In contrast, Sign is designed around the decentralized principles of Web3.
The architectural differences between Sign and traditional identity systems result in distinct approaches to data control, user sovereignty, and application interoperability, allowing each model to serve different ecosystem needs.
Risks to Consider When Investing in Sign
Although Sign demonstrates technological potential, several risks should still be considered.
- Technology Adoption Risk
Onchain attestation remains an emerging infrastructure sector, and its application scale is still developing.
If ecosystem adoption grows slowly, the protocol’s value could be affected.
- Competitive Pressure
The Web3 identity and attestation sector already includes multiple competing projects, such as:
-
DID protocols
-
Reputation systems
-
Data verification networks
Sign will need to remain competitive in both technology and ecosystem development.
- Regulatory Uncertainty
Identity and data verification systems may involve privacy and compliance considerations.
Future regulatory changes could affect the protocol’s development.
- Token Market Volatility
The price of the SIGN token may be influenced by market sentiment and liquidity conditions.
Overall, the long-term outlook for Sign depends on the real-world adoption of onchain attestation technology, competition within the ecosystem, and changes in the regulatory environment. The price of the SIGN token may also be influenced by broader movements in the cryptocurrency market.
Conclusion
Sign (SIGN) aims to solve a key challenge in the Web3 ecosystem: how to establish trusted data and identity systems in a decentralized environment. Through onchain attestations, schema structures, and cross-chain verification mechanisms, Sign converts identity, behavior, and data into verifiable credentials that can be shared across applications. This infrastructure can support Web3 identity systems while also providing technical foundations for DAO governance, onchain reputation, and airdrop verification.
Over the long term, as multi-chain ecosystems and Web3 applications continue to expand, the importance of trusted data infrastructure may grow. If Sign can achieve breakthroughs in developer adoption and real-world applications, its role within the Web3 infrastructure layer may expand further.
FAQs
Q1: What does Sign (SIGN) do? Sign is an onchain attestation protocol used to create and verify digital credentials for identity, behavior, and data.
Q2: How is Sign related to DID?
Sign can serve as infrastructure for decentralized identity (DID) systems by recording identity-related attestations.
Q3: What is the purpose of the SIGN token? SIGN is mainly used for protocol governance, ecosystem incentives, and certain network fee payments.
Q4: Does Sign support multiple blockchains? Yes. Sign is designed with cross-chain interoperability, allowing attestation data to be shared across multiple blockchain networks.
Q5: What use cases does Sign support? Sign can be used in DAO governance, airdrop verification, onchain identity systems, reputation systems, and Web3 community management.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


